miguelbazil
Ninja
As falhas só afectarão a credibilidade quando houverem ataques claros que afectem pessoas. Até lá, toda a gente vai achar que é algo teórico. Somos pouco dados à prevenção, infelizmente.

Outch!!!
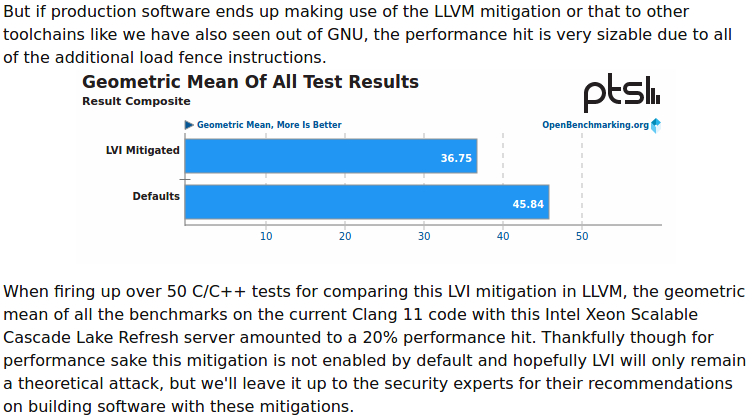
Eu espero mesmo que este LVI não seja pratico em processadores sem SGX, porque mesmo que existam aperfeiçoamentos nos patchs, este hit de performance é brutal.

https://twitter.com/Underfox3/status/1263731551252201472In this article is presented a TSX-based side channel attack, which reveals the global descriptor table and interrupt descriptor table addresses in the kernel space, and could be exploited by an arbitrary user-mode application.




CROSSTALK
For the first time, we show that speculative execution enables attackers to leak sensitive information also across cores on many Intel CPUs, bypassing all the existing intra-core mitigations against prior speculative (or transient) execution attacks such Spectre, Meltdown, etc. Until now, all the attacks assumed that attacker and victim were sharing the same core, so that placing mutually untrusting code on different cores would thwart such attacks. Instead, we present a new transient execution vulnerability, which Intel refers to as “Special Register Buffer Data Sampling” or SRBDS (CVE-2020-0543), enabling attacker-controlled code executing on one CPU core to leak sensitive data from victim software executing on a different core.

Mitigations
Intel has implemented its mitigation for the SRBDS vulnerability in a microcode update distributed to software vendors on Tuesday June 9, 2020 or earlier. The mitigation locks the entire memory bus before updating the staging buffer and only unlocks it after clearing its content. This strategy ensures no information is exposed to offcore requests issued from other CPU cores. Due to the considerable performance overhead of locking the entire system’s memory bus, Intel only applied the mitigation to harden a small number of security-critical instructions, specifically RDRAND, RDSEED, and EGETKEY (a leaf of the ENCLU instruction). This means that output from any other instruction (e.g., RDMSR) that issues offcore requests can be still leaked across CPU cores.
Straight-Line Speculation (SLS)
Arm Armv8-A core implementations utilizing speculative execution past unconditional changes in control flow may allow unauthorized disclosure of information to an attacker with local user access via a side-channel analysis, aka "straight-line speculation."
Mais um dia, mais uma vulnerabilidade para os processadores da Intel. Crosstalk.

https://www.vusec.net/projects/crosstalk/
Este ataque é interessante, porque funciona entre diferentes cores no mesmo CPU.
O fix é parcial, devido aos impactos de performance e é via microcode.
Desta vez, desligar SMT não ajuda em nada e, mais uma vez, o SGX ajuda ao ataque.
Desta vez a Intel não ficou "sozinha". Também foi descoberto um Side channel Attack em ARM.
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13844

https://www.techpowerup.com/268680/...scalation-vulnerability-affects-amd-platformsa new security vulnerability affecting certain client- and APU processors launched between 2016 and 2019. Called the SMM Callout Privilege Escalation Vulnerability, discovered by Danny Odler, and chronicled under CVE-2020-12890, the vulnerability involves an attacker with elevated system privileges to manipulate the AGESA microcode encapsulated in the platform's UEFI firmware to execute arbitrary code undetected by the operating system. AMD plans to release AGESA updates that mitigate the vulnerability (at no apparent performance impact)
www.tomshardware.com/amp/news/amd-radeon-gpu-steal-data-radio-transmission-cybersecurityThe researcher accomplished the feat by manipulating the graphics card's shader clock rates to become a tunable radio device.
Há coisas melhores e mais rebuscadas ainda...
A nível empresarial, de grande dimensão, a Intel deve andar a oferecer grandes descontos em novas aquisições aos maiores clientes e/ou a pagar compensações.Eu nao sei como a nivel empresarial isto não esta a dar mais salgalhada, ou entao ninguem anda a aplicar patchs.